Resources
This Refund Costs Money
In this week’s scam, you receive an email that appears to be from Microsoft. The email says that you have purchased a subscription to one of Microsoft’s products. It seems legitimate because it is sent from a Microsoft domain, has a genuine order number in the text, and even contains official logos.
The email claims that you bought an expensive Microsoft subscription and gives a number to call for a refund if you didn't make the purchase. But this email and the support phone number aren't real. If you call the number, scammers posing as Microsoft support will likely ask you for your login and bank account information. You never actually paid for any Microsoft products, but if you call the fake phone number, you will pay the scammers!
Follow these tips to avoid falling victim to a phishing scam:
- You should always be suspicious if an unsolicited email asks you to call a phone number. Microsoft would never request that you call a phone number for a refund.
- If you have concerns about a purchase, always go directly to Microsoft's official website.
- Always be cautious when you receive unexpected emails about account problems, security alerts, or purchases. These emails can be a setup for a phishing scam.
It’s tax season in many countries, and cybercriminals are trying to take advantage of this. In this week’s scam, cybercriminals are targeting Pakistani taxpayers. They are sending phishing emails containing attachments that appear to be official tax documents. The email includes an attachment that appears to be an official tax form from the Pakistani government.
Opening this fake file will install malware on your computer. The malware uses Microsoft Management Console (MSC) files, which can be used to run scheduled tasks on your computer. Because the malware uses scheduled tasks, it can stay active for a long time, even if you reboot your computer. This malware will infect your computer, gather your sensitive information, and steal your data. Your taxes won't be paid, but the cybercriminals will!
Follow these tips to avoid falling victim to a malware phishing scam:
- Avoid downloading attachments from unexpected emails. Only download attachments and documents from sources you trust.
- This attack targets Pakistani taxpayers, but remember that cybercriminals can use similar methods to target residents of any country.
- Always access and download tax-related forms from official financial or government websites. When in doubt, visit an official tax-related website.
Scammers will frequently use high-profile events, such as natural disasters, to try to trick you. In the aftermath of Hurricane Helene in the United States, scammers have wasted no time in turning this situation to their advantage. They've been using AI to generate fake images that play on your emotions, to get you to donate your money to help people who have been affected by the disaster. Recently, an image of a scared little girl holding a puppy and being evacuated from a flood area has been circulating on Facebook and other social media.
However, this image is fake. The scammers are trying to trick you into clicking a link to "donate" to a fake relief effort or to steal your personal information. In either case, their goal is to get you to act impulsively. If you donate money or enter any personal information, it will not help any victims who were impacted by the hurricane. However, it will help the scammers steal your money and your data!
Follow these tips to avoid falling victim to a hurricane scam:
- Be wary of AI-generated images. Look for signs that an image might be fake, such as unusual details or inconsistencies.
- Make sure that the charity you’re donating to is legitimate. Only donate through the official websites of well-known charitable organizations.
- Don't act impulsively. Take time to research before donating or clicking on links, especially in the aftermath of a disaster.
Here is how it works:
Did you get a message on social from an “artist” asking to pay you for permission to paint your photo? It’s a scam. They don’t want to pay you — they want to take your money.
Young adults report this scam begins with a direct message on social media from someone who says they like your photo and want to pay you thousands of dollars to use it. Next, they’ll send you a check. They’ll tell you to deposit it, take some money out to send to the artist for supplies, and keep the rest. They may promise to reimburse any money you send back. (But they never will because it's a scam.)
While the check may look real and the funds may initially show up in your bank account, the check’s fake. By the time the bank realizes it, you’ll be out the money you sent the scammer and owe the bank any money you withdrew.
How do you spot this scam? Here’s the takeaway: If someone you don’t know sends you a check and asks you to send money back to them or to someone else, it’s a scam. It’s best to only deposit checks from people you know and trust.
If you spot a scam, report it at ReportFraud.ftc.gov. And if you think you’ve paid a scammer, here's what to do.
You may not think too much about downloading an app onto your phone. Apps are widely available and can make navigating a website from your phone much easier. However, many people may not realize that they can also be used by cybercriminals to steal your information. In this week’s scam, cybercriminals are targeting Android devices with malicious apps. The apps include a fake Google Chrome app and a fake sports streaming app called 4K Sports.
If you download these apps, malware will be installed on your phone. Cybercriminals design this malware to allow them to access your phone without you knowing about it. This malware can record what you type into your phone or allow cybercriminals to control your phone remotely. It can even access your phone contacts and send them text messages. The texts contain links to web pages with malicious apps available for download, allowing the malware to continue to spread.
Follow these tips to avoid falling victim to a phishing scam:
- Only download apps from official and trusted sources like the Google Play Store or the Apple App Store. Avoid downloading apps from third-party websites or links sent via text or email.
- Read reviews and do research before downloading any app, especially lesser-known ones.
- Don't click on suspicious links in unexpected text messages or emails, even if they appear to come from someone you know.
Fake Login Fiasco
Scammers frequently try to trick you into clicking on malicious links in emails by making them appear legitimate. In a recent scam, they are trying to trick you with an email that appears to be related to your Microsoft account security. The email says that there has been some unusual activity on your account and that many of your account’s features have been locked. There is a link in the email, along with instructions to click it so that you can review all activity on your account.
If you click the link, you’ll be taken to what appears to be a Microsoft login page. However, the login page is actually fake, and you won’t be taken to your Microsoft account if you enter your login information here. Instead, entering your user credentials on this page will allow cybercriminals to steal them. Once they have your username and password, they can use them to access your account and steal your personal information.
Follow these tips to avoid falling victim to a phishing scam:
- Scammers will often try to scare you into acting impulsively. Always stop and think before clicking, especially if an email is instructing you to act quickly.
- Pay attention to the details of the email. Phishing emails will often contain spelling and grammatical errors, or the wording of the email may seem unusual.
- Navigate to the official website in your browser whenever possible. Clicking a link in an email may direct you to a fake or malicious website.
In this week’s scam, cybercriminals are spreading malware by using a fake security app. They send you a text message that says a large financial transaction has just occurred using your bank account. It instructs you to call a phone number if you have not authorized the transaction. Of course, the transaction never occurred, and the cybercriminals are trying to scare you into acting impulsively.
If you dial the number, you’ll be connected to a cybercriminal who will instruct you to download a security app. The app is disguised as an official McAfee Security product and is designed to take control of your device. If you install it, cybercriminals will use it to steal your data, and they will have complete control of your phone. Once they have control of your phone, they can install other malware and access your personal information.
Follow these tips to avoid falling victim to a fake app scam:
- Only download apps from an official source, such as the Google Play Store or the Apple Store. Apps available on official platforms are tested for security and are far less likely to be malicious.
- If you receive an unexpected text message regarding a large transaction, contact your bank directly using the information provided on their official website. Do not communicate using the information provided in the text message.
- Always stop and think before taking action. Scammers use scare tactics to create a sense of urgency to get you to act without thinking.
IMPORTANCE OF SOFTWARE UPDATES
If the FMB app isn't working on your phone, tablet, or other device, it's likely because you have not updated the software and it is no longer secure. Compatibility information can be verified from the device by going to the App or Google Play store.
Software updates are important for numerous reasons.
*They improve the phone’s functionality and make it much more efficient. Updated phones do not usually experience compatibility issues with the latest software either, so you can download or use the latest versions of any application you like with ease.
*New features gained through updates improve the phone’s stability and usability. *The most important reason to update your phone is that this practice can constantly enhance your phone’s security features and help keep you safe from cybercriminals and viruses.
Make sure to update your mobile device software regularly.
Have you noticed any suspicious PDF attachments in your Microsoft Outlook recently? There has been a surge in phishing emails with PDF attachments sent to Outlook users over the last several months. Many of these emails are Amazon-themed phishing scams that are focused on targeting Outlook users in North America, Southern Europe, and Asia.
In this scam, cybercriminals are posing as Amazon support and sending notifications claiming that your Amazon account is on hold due to billing errors. The email urges you to resolve this issue by clicking a link to update your billing information. The cybercriminals cleverly hide their malicious intent behind URL shorteners and other tricks, making these unsafe links hard to spot. If you click one of these links, you’ll be sent to a fake website designed to steal your login credentials or credit card information. The PDF files attached to these phishing emails also contain malware, which can cause security risks if you download them to your device.
Follow the tips below to stay safe from similar scams:
- Always be suspicious of unexpected emails, particularly if they ask for personal or financial information.
- If you receive an email claiming that you need to verify information on your account, navigate directly to the official website instead of clicking on a link.
- This attack isn't exclusive to Outlook users. Anyone who uses email can be exploited, so be careful with the emails you receive.
Learn How to Avoid Gift Card Scams
Check Fraud
Fraudsters are continually finding new ways to defraud consumers with fraudulent checks. Here are some tips to help you keep your accounts safe.
In an age where digital is all the rage, fraudsters are using a classic financial tool to gain access to your funds: Paper Checks
One of the most common tactics driving this rise in check fraud is mail theft. Fraudsters are stealing mail, looking for checks, then selling these checks to others – sometimes on the dark web. FinCEN issued an alert earlier this year, warning about a nationwide surge in mail theft-related check fraud schemes.
Here are some common methods a scammer might use to commit fraud with a stolen check:
- Check Altering: Sometimes called “check washing,” a scammer may use common household chemicals to change the printed dollar amount and payee name on a check.
- Creating counterfeit or duplicate checks: By using the information on the stolen check, fraudsters may further exploit the victim’s account information by creating additional counterfeit copies of the check.
- Forging endorsements and engaging in identity theft: Typically, your name and address is found on a check. Criminals may use that information to steal your identity.
What can you do to protect yourself from mail theft and check fraud?
Fortunately, there are steps you can take to help reduce your risk of being taken advantage of by someone engaging in a mail theft-related check fraud scheme. Keep these tips in mind to help protect yourself from check fraud when sending money to others:- Set-up Online Account Alerts. Use our online transaction and account alerts to notify you via text or email when debit items clear or your balance is low. These can help catch fraud sooner if it occurs. Go to Manage Alerts in Online Banking or your FMB Mobile App to set them up today!
- Pay digitally. Reduce the number of checks you send and utilize digital payment methods instead. Use FMB’s Person to Person payment option within Online or Mobile Banking to send money to people securely.
- Use the FMB Online Bill Pay. We will always send your payments electronically, when possible, for the payee. If a check is mailed using Online Bill Pay, the payment information be printed onto the check making it harder to alter.
- Use a gel pen. If you write a check, be sure to use a black gel pen. The ink is more difficult to remove.
- Use mailboxes that are secure. If you need to send any checks by mail, use the mailbox inside of a USPS facility rather than at a curbside USPS mailbox or your residential outgoing mail.
- Keep your bank account information safe. Do not share or post your bank account information anywhere publicly, and never share account information with anyone with whom you did not initiate the communication. Make sure when you do enter your account number online that the URL has a https: The “s” means it’s secure. Do not allow websites to save your routing/transit and account number information.
- Don’t use window envelopes. Avoid using window envelopes when mailing checks. Window envelopes aren’t necessarily unsafe; however they can alert would-be thieves to the importance of the contents.
- Use Positive Pay. Positive Pay is a fraud prevention tool your business can use to monitor check and ACH activity. It matches the items clearing your account to your company’s issued checks. This is an additional service in Online Banking that businesses must enroll in. Contact your branch to enroll.
Putting these tips into place can help you avoid becoming the victim of a check fraud scheme. Contact your branch today for assistance is setting up Online Alerts, Bill Pay, or Person to Person payments.
Recently, cybercriminals have been impersonating postal services around the world through SMS phishing (smishing) scams. These postal services include the US Postal Service, UK Royal Mail, Correos in Spain, and Poste Italiane in Italy.
In this scam, cybercriminals send you a text message impersonating the postal service in your country. The text contains a link and says that your package can’t be delivered until you provide additional information. If you tap the link, you’ll be taken to a spoofed postal service website that prompts you to enter your credit card details so your package can be delivered. If you enter your credit card details, cybercriminals could steal your money or personal information.
Follow the tips below to stay safe from similar scams:
- Never tap a link in a text message that you weren’t expecting.
- Be cautious when entering payment information on a website accessed via text message. To stay safe, navigate directly to the organization's official website.
- Remember that this type of attack isn’t exclusive to postal services. Cybercriminals could use this technique to impersonate any business in any country.
New scams originating from fake ads on social media increase daily. Here's what you need to know to protect yourself.
Even legitimate ads are copied and repurposed, and as a user, you have no way of knowing whether the ad is legitimate. Don’t click on it! Attackers can disguise their domains, so you won’t know where an ad will take you.
Because online scams and Facebook Marketplace scams are so widespread it’s important to learn how to identify a scammer. What are some red flags that it’s a scam?
The ad is too good to be true….
Sometimes, deals that seem too good to be true are legitimate, but more often, they’re not. Fake ads on social media are often hard to identify, which means, “The old saying, ‘If it seems too good to be true, it probably is,’ always applies to online ads.
Look for urgent language like “limited time offer” or “only a few left,” both of which are signs of fake ads on social media.
The price point is ridiculously low….
Massive discounts on branded items are a sign that this is a fake ad on social media. If the ad promises you valuable, high-demand brand apparel, beauty products, electronics, luxury goods or rare collectibles at a price point that’s absurdly lower than everyone else’s, it’s probably either a counterfeit product or a counterfeit store.
The URL doesn’t begin with https://...
If you’ve been taken to a website, check the URL. If it doesn’t begin with https://, that’s a red flag, and they could be running an online shopping scam. The ‘s’ indicates encryption security on the site. If you see an ad that sends you to a website that’s http, be extra careful, it could be a fake or counterfeit site. Most reputable e-commerce sites begin with https. Rather than clicking on an ad to see its deal, Google and find the brand’s legitimate website. Then manually search for the deal you saw, says Hauk.
It asks for your card information first….
Stop right there! It’s a red flag if your payment information comes before other details. Never submit your personal information or share your card or account info with these social media accounts or websites.
You are unable to comment on the photo….
If the account has comments turned off, it could be a fake ad. There are some cases when a legitimate account may turn off comments—when it’s a scam, comments are usually turned off because they don’t want to invite questions or complaints about the product they ordered that never arrived. Social media scammers want to limit your interaction with them once they have your information.
There are too many five-star reviews….
Too many high rated reviews is a red flag and cause for concern especially if the reviews are attached to a too-good-to-be-true offer.
There are very few hashtags….
Hashtags serve various purposes, but the ultimate goal is to reach more people and drive traffic to the company’s social media or website. Check for a sponsored tag. Some ads on Instagram have a sponsored tag on top of them to differentiate them from other posts. This is a sign the social media ad is legitimate.
It’s summertime in the northern hemisphere, so you know what that means: phishing trips! Recently, statistics from Check Point Research showed an increase in vacation-themed website domains. Of the domains found, an estimated one in every 83 was malicious or suspicious. Cybercriminals use phishing scams to direct you to these dangerous domains.
In one of these summer-themed scams, cybercriminals impersonate your organization’s HR department. They send a fake email announcing a new open vacation plan that only some employees are eligible for. Then, the email directs you to click a link to find out if you are one of those eligible employees. If you click the link, you will be directed to enter your work email and password. Entering your credentials on this page will give cybercriminals easy access to your work email and the organization as a whole.
Follow the tips below to stay safe from similar scams:
- The weather may be different in your part of the world, but that won’t stop cybercriminals from using this tactic. Look for red flags such as an email sent outside of your local work hours.
- This specific scam is designed to make you feel curious, concerned, and even frustrated. Don’t let cybercriminals play with your emotions. Think before you click.
- If you receive an unexpected email from HR, verify the legitimacy with someone in your organization. Don’t reply to the email. Instead, contact your manager or a point person in HR directly.
You may not be able to tell right away if an incoming call is spoofed. Be extremely careful about responding to any request for personal identifying information.
- Don't answer calls from unknown numbers. If you answer such a call, hang up immediately.
- If you answer the phone and the caller - or a recording - asks you to hit a button to stop getting the calls, you should just hang up. Scammers often use this trick to identify potential targets.
- Do not respond to any questions, especially those that can be answered with "Yes" or "No."
- Never give out personal information such as account numbers, Social Security numbers, mother's maiden names, passwords or other identifying information in response to unexpected calls or if you are at all suspicious.
- If you get an inquiry from someone who says they represent a company or a government agency, hang up and call the phone number on your account statement, in the phone book, or on the company's or government agency's website to verify the authenticity of the request. You will usually get a written statement in the mail before you get a phone call from a legitimate source, particularly if the caller is asking for a payment.
- Use caution if you are being pressured for information immediately.
- If you have a voice mail account with your phone service, be sure to set a password for it. Some voicemail services are preset to allow access if you call in from your own phone number. A hacker could spoof your home phone number and gain access to your voice mail if you do not set a password.
- Talk to your phone company about call blocking tools and check into apps that you can download to your mobile device. The FCC allows phone companies to block robocalls by default based on reasonable analytics. More information about robocall blocking is available at fcc.gov/robocalls.
Remember to check your voicemail periodically to make sure you aren't missing important calls and to clear out any spam calls that might fill your voicemail box to capacity.
Don't let your guard down just because you're on a mobile device. Be just as careful as you would on a desktop! Hackers have multiple ways of getting personal information through WiFi, Apps, Browsers, Bluetooth, Smishing (phishing via SMS), and Vishing (voice phishing).
Learn 20 Ways to Block Mobile Attacks
Visit the FDIC's site for more information
During times of economic change, cybercriminals will use fear and instability to their advantage. Now, they’re using concerns about energy costs to lure victims into their malicious scams. These scams offer rebates, refunds, or discounts for energy bills to appeal to frustrations about rising costs.
In a recent scam, cybercriminals send you an email offering you a refund on your latest energy bill. The email includes a link to a website where you’re asked to provide personal information, such as your bank account credentials, in order to receive the refund. If you share this information with cybercriminals, they can steal your money and target you in future scams.
Don’t fall for these scams! Follow the tips below to keep your information safe while keeping your lights on:
- Cybercriminals often use urgent deadlines and scare tactics to trick you into sharing sensitive information. Always think before you click.
- If an offer sounds too good to be true, it probably is. Verify any offers of rebates, refunds, or discounts by visiting your energy provider’s official website.
- Before you click on a link, hover your mouse over it. Make sure that the link leads to a legitimate, safe website that corresponds with the content in the email.
Multi-factor authentication (MFA) provides an extra layer of security for your accounts, but it’s important to think before you click. Cybercriminals can use an attack method called MFA prompt bombing to get around MFA protections and overwhelm you with prompts via email, text message, or phone call.
For example, cybercriminals may attempt to log in to an account using your credentials. Then, they’ll request a phone call MFA verification, which is sent to the phone number you use for MFA. Cybercriminals will often request these verifications late at night when you’re asleep and unprepared. If you accept the phone call and press the button to verify your identity, you may grant the cybercriminals access to your account. Once the cybercriminals bypass your MFA, they can use your account to achieve their malicious goals.
Don’t let MFA give you a false sense of security. Follow the tips below to stay safe from MFA prompt bombing scams:
- Never approve an MFA notification you didn’t request. If you have a shared account, verify the MFA request with the other account holder before taking action.
- If you receive an MFA notification you didn’t request, immediately change your password for the associated account. You should also consider updating your passwords for any accounts that use the same credentials.
- Create unique, strong passwords for each of your accounts. Without your password, it’s difficult for cybercriminals to reach the MFA step of the login process.
UK residents are targets of a recent smishing (SMS Phishing) scam. In this scam, cybercriminals impersonate the home delivery company, through fake failed delivery text messages that include a link to reschedule the delivery.
The link included in these fake delivery notifications leads to a phony look-alike website. On the website, you're asked to provide your personal and financial information to reschedule the delivery. Unfortunately, if you fill out and submit this form, you won't be receiving any packages. Instead, you'll be delivering your sensitive information right to the cybercriminals.
Follow these tips to protect yourself from similar smishing attacks:
- Think before you tap. Are you expecting a package? Have you signed up for text notifications? Is this like notifications you’ve received before from this company?
- Never tap on a link in an email or text message that you were not expecting. Instead, open your browser and enter the official URL for the website you wish to visit.
To verify the legitimacy of a delivery notification, contact the company by phone, email, or their official mobile app. Do not use the phone number or link sent in the text to contact the company.
What could be safer than sending money to yourself through your own bank?
A new social engineering scam is making the rounds, and this one is particularly insidious: It tricks users into sending money to what they think is their own account to reverse a fraudulent charge.
The FBI's Internet Crime Complaint Center issued the warning, which it said involves cybercriminals who have definitely done their homework. "In addition to knowing the victim's financial institution, the actors often had further information such as the victim's past addresses, social security number, and the last four digits of their bank accounts," the IC3 said.
The con starts off as many that target individuals do nowadays: With a text message. In this case it's not a phishing attempt, it's an attempt to ascertain whether the person receiving the message is susceptible to further manipulation. Posing as the target's bank, the message asks whether a large charge ($5,000 in the example the FBI gives) was legitimate and asks for a reply of YES or NO. Replying no leads to a follow-up text: "Our fraud specialist will be contacting you shortly.
This is where social engineering comes in, and the FBI is painting a picture of a sophisticated operation.
The "fraud specialists" contacting users reportedly "speak English without a discernible accent," and once they establish credibility with the victim they move on to "helping" them "reverse" the fake transaction.
It gets even more insidious here: The charges that are being refuted aren't bank charges directly: they are payments being made through an instant payment app like Venmo or CashApp. The fraudster never asks for a password or any information that might clue someone in that they're being strung along.
Instead, the caller asks the victim to use their bank website or app to remove their email address from the digital payment app (thereby unlinking the app and bank account), which the fraudster then asks for. Next, the victim is asked to send the same amount as the fake payment to themselves using their own email address, which has already been added to an account the criminal controls.
"Victims often only realized they had been scammed after they checked their financial account's balance," the FBI said.
The FBI says that the normal tips for avoiding phishing apply here: Don't respond to unsolicited requests to verify information, if you receive one contact your financial institution directly, keep MFA enabled on all accounts and be wary of anyone providing personally identifiable information as proof of their legitimacy. Also, the FBI said, "financial institutions will not ask customers to transfer funds between accounts in order to help prevent fraud."
Social engineering has been a problem on the internet dating back almost to its inception, and it treats digital crime in the same way that crimes in the physical world are planned: What's the path of least risk with greatest reward?
Online, it's less about brute force or technical skill, both of which require knowledge, training and time, and more about con artistry, which is made simpler in the digital world where personal charisma is less essential.
Those who've yet to come in contact with a social engineering attack are a rapidly shrinking pool: According to one statistic, 98 percent of cyber attacks involve social engineering in some capacity.
Recruitment websites are a great way to find new job opportunities. Unfortunately, very few of these recruitment websites properly validate the people posting jobs, which makes it surprisingly easy to create fake job posts.
Cybercriminals have been creating fake job posts that appear to be listed by a legitimate organization. These fake posts direct you to contact a malicious email address, phone number, or website that appears to belong to the spoofed organization. Cybercriminals use this scam to try to steal your personally identifiable information. This type of information is often provided when applying for a job, which makes this scam simple, yet effective.
Follow the tips below to stay safe from these types of scams:
- Watch out for grammatical errors, unusual language, and style inconsistencies in job posts. Be suspicious of job posts that look different compared to other job posts from the same organization.
- Avoid applying for a job within a recruitment website’s platform. Instead, look up the organization’s official website and find their careers page.
- Cybercriminals could also use this scam to target people within a specific organization. Be sure to follow your organization’s specific guidelines when applying for internal positions.
It’s that time of year – love is in the air and Valentine’s Day is approaching!
Many Americans dream of finding their one true love and, in the world of technology, many are turning to online platforms to find that special someone. Common online platforms include (but are not limited to) email, social media, dating apps and dating websites. While one person’s intentions may be to find love, unfortunately scammers often prey on hopeless romantics for financial gain.
Romance scammers typically create fictitious profiles with attractive pictures and personal information lifted from internet searches or the social media profiles of real people. Within a short period of communication, the scammer is likely to claim they need money for one reason or another.
These scams happen to everyday people, including your friends, family, and clients.
The Lies Romance Scammers Tell
Scammers often say they’re living or traveling outside of the United States. They commonly say they are:
- Working on an oil rig
- In the military
- A doctor working for an international organization
Romance scammers often ask their targets for money to:
- Pay for a plane ticket or other travel expenses
- Pay for surgery or other medical expenses
- Pay customs fees to retrieve something
- Pay off gambling debts
- Pay for a visa or other official travel documents
Scammers ask people to pay by:
- Wiring money
- Using reloadable cards like MoneyPak
- Purchasing gift cards from vendors like Amazon, Google Play, iTunes or Steam
Scammers prefer these payment methods because they can get cash quickly and remain anonymous. They also know the transactions are almost impossible to reverse.
How To Avoid Losing Money to a Romance Scammer
Here’s the bottom line: you should never send money or gifts to a sweetheart you haven’t met in person.
If someone you care about suspects they are involved in a romance scam, here are a few tips to pass along:
- Stop communicating with the person immediately.
- Encourage them to talk to someone they trust and pay attention if their friends or family say they’re concerned about their new love interest.
- Suggest they search for the type of job the person has to see if other people have heard similar stories. For example, they could search for “oil rig scammer” or “U.S. Army scammer.” They can also browse the comments on the Federal Trade Commission’s blog posts about romance scams to hear other people’s stories:
- Faking it – scammers’ tricks to steal your heart and money
- Has an online love interest asked you for money?
- Romance scams will cost you
- Suggest they conduct a reverse image search of the person’s profile picture to see if it’s associated with another name or with details that don’t match up – those are signs of a scam.
Reporting a Romance Scam
- Contact your financial institution right away if your account information or online banking credentials have been compromised or have been involved in a scam.
- If you paid a romance scammer with a gift card, contact the company that issued the card right away. Let the company know you paid a scammer with the gift card and ask if they can refund the money.
- If you believe they’ve been a victim of a scam, report it to the FTC at ReportFraud.ftc.gov. You should also notify the website or app where they met the scammer, too.
Being the victim of a romance scam is a sad reality for so many and is heartbreaking both emotionally and financially.
Netflix is both the world’s largest streaming platform and one of the most impersonated brands among cybercriminals. There have been many Netflix-themed scams over the years, but most of these scams target one of two groups: current Netflix subscribers or potential Netflix subscribers.
To target current Netflix subscribers, cybercriminals send phony email notifications claiming there is a problem with your billing information. To target potential Netflix subscribers, cybercriminals send emails that advertise a deal for new accounts. Both phishing emails include links that lead to Netflix look-alike webpages where you’re asked to provide your personal and payment information. Any information you enter on these fake webpages is delivered straight to the cybercriminals.
Remember the tips below to stay safe from streaming scams:
- Never click on a link within an email that you weren’t expecting, even if the email appears to come from a company or service you recognize.
- These types of scams aren’t limited to Netflix. Cybercriminals also spoof other streaming services, such as Disney+ and Spotify. Remember that if a deal seems too good to be true, it probably is.
- If you receive an unexpected notification, open your browser and navigate to the platform’s website. Then, you can log in to your account knowing that you’re on the platform’s real website and not a phony look-alike website.
A recent proposal in Washington would require banks to report to the IRS on the inflows and outflows of all accounts worth over $600. Under the proposal, Farmers and Merchants Bank would be required by the government to report your account information to the IRS.
We care about you and your privacy and want you to know about this potential change proposed by Washington policymakers. If you want to learn more about these issues or share your opinion with Congress, visit banklocally.org/privacy.
Let Congress know your privacy matters by filling out the form linked below.
If you’ve started your holiday shopping, you may have received purchase confirmation emails from Amazon, one of the world’s most popular retailers. Unfortunately, cybercriminals have also been sending their own version of these emails. In a new scam, cybercriminals impersonate Amazon to send fake purchase confirmation emails in hopes of receiving a special holiday gift: your credit card information.
In this scam, cybercriminals send you a fake purchase confirmation email that appears to come from Amazon. In the email, you can review details about the phony purchase, such as the payment amount and your mailing address. To review the purchase further, you can click a “View or manage order” button in the email. If you click this button, you’ll be taken to Amazon’s real website, but you won’t be able to find information about the purchase. As a last resort, you can call the customer service phone number in the email. If you call, you’ll be asked to provide your credit card number and CVV number to cancel the purchase. Instead of canceling the purchase, you’ll grant cybercriminals access to your credit card.
Don’t fall for this scam! Follow the tips below to stay safe:
- Watch out for fake customer service phone numbers. If you need assistance, check the vendor’s website to find their customer service phone number or email address.
- Don’t click links in emails you weren’t expecting. If you click a malicious link, malware or other malicious software may be downloaded onto your device.
- Don’t share sensitive information, such as credit card numbers or social security numbers, over the phone.
It’s only early November, but you have probably already seen Christmas trees sold in stores. This is a trend known as “seasonal creep” in which retailers start selling seasonal items in advance of the actual season. Did you know that cybercriminals also follow this trend?
For example, Black Friday and Cyber Monday traditionally fell after Thanksgiving in the United States. However, these international shopping events now start as early as November 1. Cybercriminals take advantage of this trend by sending phishing emails disguised as advertisements and phony purchase receipts long before the holiday season begins.
Follow the tips below to shop safely this holiday season:
- Never click a link from an email or text message that you weren't expecting, even if the link appears to be for a store you recognize. Instead, use your browser to navigate directly to the retailer’s official website.
- Watch out for malvertising. Malvertising is when cybercriminals try to phish shoppers through ads on social media and other websites. Always think before you click!
- Be cautious of advertisements that promise outrageous deals. Remember that if something seems too good to be true, it probably is!
In a recent scam, cybercriminals impersonated the telecommunications provider, Verizon. The logo for Verizon is the company name, followed by a red asymmetrical “V” that resembles a check mark. Cybercriminals imitated this logo by using mathematical symbols, such as the square root symbol (√).
Using their fake logo, cybercriminals sent a phishing email that was disguised as a Verizon voicemail notification. The email directs you to click the “Play” button to listen to the voicemail. If you click the button, you are taken to a phony look-alike Verizon webpage. Before you can listen to the voicemail, you are directed to log in to your Microsoft Office 365 account for authentication. Unfortunately, if you enter your credentials, you’ll give the cybercriminals full access to your Microsoft Office 365 account.
Use the tips below to stay safe from similar scams:
- This type of attack isn’t exclusive to Verizon. Cybercriminals could easily use this technique for other brands. Always think before you click.
- Watch out for anything out of the ordinary. A Verizon webpage asking you to log in using your Microsoft Office 365 account is quite unusual.
- If you receive an unexpected notification, open your browser and navigate to the provider’s website. Then, you can log in to your account knowing that you are on the real website and not a phony look-alike website.
FinCEN has issued an advisory regarding Imposter Scams and Money Mule Schemes in relation to the Coronavirus. Please check the links below for more information on these scams to keep up to date on how to protect yourself:
In a new Smishing (SMS Phishing) attack aimed at Android users, cybercriminals send a text message that claims you have a delivery that needs to be paid for. If you tap on the link provided in the text, you are taken to a page that asks you to update your Google Chrome app. If you tap the Install Now button on the page, a download begins and you are redirected to a payment screen. On this screen, you are asked to pay a small fee so that your package can be delivered. If you provide any payment information on this page, it is sent directly to the bad guys.
Unfortunately, this scam gets worse. If you tapped the Install Now button mentioned above, you actually downloaded malware that uses the icon and name of Google Chrome to disguise itself. This “app” then uses your mobile number to send thousands of smishing texts to random, unsuspecting victims.
Don’t become a part of their scam! Follow the tips below to stay safe from attacks like this:
- Only download and update apps through your device’s official app store.
- Though this attack targets Android users, this technique could be used on any kind of mobile device, so always be suspicious of unexpected text messages.
- If you are expecting a package, stay up-to-date on your order by visiting the retailer’s official website and not by tapping a link in a text message.
Stop, Look, and Think. Don't be fooled.
A romance scam is when a new love interest says they love you, but they really just love your money—and may not be who they say they are.
Be on the lookout for these romance scams:
- A new love who lives far away asks you to wire them money or share your credit card number with them—even if they say they’ll pay you back.
- Your new romantic interest asks you to sign a document that would give them control of your finances or your house.
- Your new sweetheart asks you to open a new joint account or co-sign a loan with them.
- Your new darling asks for access to your bank or credit card accounts.
Report in-person romance scams to local law enforcement. Report online romance scams to ftc.gov/complaint.

An easy way for cybercriminals to get your attention is to claim that you owe a large amount of money. Pair this claim with a QuickBooks-themed phishing email and malicious malware, you get a dangerous cybersecurity threat.
The cybercriminals send a well-made spoof of a QuickBooks email that even includes an invoice number. The email message states that you owe over one-thousand dollars for the order but it gives no further details. Attached to the email is what appears to be an Excel file with the invoice number as the filename. The bad guys are hoping you’ll open the attachment looking for more information. If you do open it, you’ll actually be opening a dangerous piece of malware specially designed to target your financial and banking information. This malware can lead to unauthorized charges, wire transfers, and even data breaches.
Here’s how you can stay safe from scams like this:
- Never click a link or download an attachment in an email that you were not expecting.
- Remember that bad guys can disguise anything, even file types.
- If you think the notification could be legitimate, navigate to the official QuickBooks website and log in to your account to confirm.
A new Smishing (SMS Phishing) attack uses an urgent text message to trick you into clicking a malicious link. The message states “PayPal: We've permanently limited your account, please click link below to verify.” If you click on the link provided, you are taken to a PayPal look-alike page and asked to log in.
Bad actors take this scam one step further. If you enter your login credentials on their phony page, you’ll be taken to a second page that asks for your name, address, and bank account details. Everything entered on these pages will be sent directly to the bad guys.
While this is an advanced attack, you can still stay safe by practicing the tips below:
- Check for poor grammar in supposedly-official messages. Did you catch the grammatical error in the example above? It asks you to “click link below” instead of “click the link below”.
- Question the situation. For example, did you give PayPal your mobile number? And did you ever sign up to receive text notifications?
- Never trust a link in a text message that you were not expecting. If you think the notification could be legitimate, navigate to the official website and log in there.
We have recently seen an increase in COVID-19 themed phishing emails sent to customers. The most recent attempt is a phishing campaign impersonating the Small Business Administration (SBA).
This is a malicious attempt to lure business owners to apply for the Paycheck Protection Program (PPP) by clicking on the provided link.
In this example, the sender posed as the President of World Trade Finance and directed the recipient to click on the embedded URL in the body of the email to fill out a registration form.
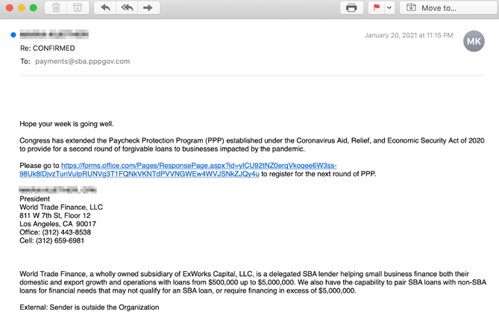
If you receive an email resembling the one shown above, DO NOT click any of the links or attachments, and DELETE it immediately.
As always, FMB strongly recommends opening email and attachments from trusted sources only.
The FTC is getting reports about people pretending to be from the Social Security Administration (SSA) who are trying to get your Social Security number and even your money. In one version of the scam, the caller says your Social Security number has been linked to a crime (often, he says it happened in Texas) involving drugs or sending money out of the country illegally. He then says your Social is blocked – but he might ask you for a fee to reactivate it, or to get a new number. And he will ask you to confirm your Social Security number.
In other variations, he says that somebody used your Social Security number to apply for credit cards, and you could lose your benefits. Or he might warn you that your bank account is about to be seized, that you need to withdraw your money, and that he’ll tell you how to keep it safe.
But all of these are scams. Here’s what you need to know:
- The SSA will never (ever) call and ask for your Social Security number. It won’t ask you to pay anything. And it won’t call to threaten your benefits.
- Your caller ID might show the SSA’s real phone number (1-800-772-1213), but that’s not the real SSA calling. Computers make it easy to show any number on caller ID. You can’t trust what you see there.
- Never give your Social Security number to anyone who contacts you. Don’t confirm the last 4 digits. And don’t give a bank account or credit card number – ever – to anybody who contacts you asking for it.
- Remember that anyone who tells you to wire money, pay with a gift card, or send cash is a scammer. Always. No matter who they say they are.
If you’re worried about a call from someone who claims to be from the Social Security Administration, get off the phone. Then call the real SSA at 1-800-772-1213 (TTY 1-800-325-0778). If you’ve spotted a scam, then tell the FTC at ftc.gov/complaint.
Coronavirus: Scammers follow the headlines
Scammers are taking advantage of fears surrounding the Coronavirus. They’re setting up websites to sell bogus products, and using fake emails, texts, and social media posts as a ruse to take your money and get your personal information.
The emails and posts may be promoting awareness and prevention tips, and fake information about cases in your neighborhood. They also may be asking you to donate to victims, offering advice on unproven treatments, or contain malicious email attachments.
Here are some tips to help you keep the scammers at bay:
- Don’t click on links from sources you don’t know. It could download a virus onto your computer or device. Make sure the anti-malware and anti-virus software on your computer is up to date.
- Watch for emails claiming to be from the Centers for Disease Control and Prevention (CDC) or experts saying that have information about the virus. For the most up-to-date information about the Coronavirus, visit the Centers for Disease Control and Prevention (CDC) and the World Health Organization (WHO).
- Ignore online offers for vaccinations. If you see ads touting prevention, treatment, or cure claims for the Coronavirus, ask yourself: if there’s been a medical breakthrough, would you be hearing about it for the first time through an ad or sales pitch?
- Do your homework when it comes to donations, whether through charities or crowdfunding sites. Don’t let anyone rush you into making a donation. If someone wants donations in cash, by gift card, or by wiring money, don’t do it.
- Be alert to “investment opportunities.” The U.S. Securities and Exchange Commission(SEC) is warning people about online promotions, including on social media, claiming that the products or services of publicly-traded companies can prevent, detect, or cure coronavirus and that the stock of these companies will dramatically increase in value as a result.
Want more information on the latest scams we’re seeing? Sign up for our consumer alerts from the Federal Trade Commission. If you come across any suspicious claims, report them to the FTC at ftc.gov/complaint.
How to Avoid Spoofing
You may not be able to tell right away if an incoming call is spoofed. Be extremely careful about responding to any request for personal identifying information.
- Don't answer calls from unknown numbers. If you answer such a call, hang up immediately.
- If you answer the phone and the caller - or a recording - asks you to hit a button to stop getting the calls, you should just hang up. Scammers often use this trick to identify potential targets.
- Do not respond to any questions, especially those that can be answered with "Yes" or "No."
- Never give out personal information such as account numbers, Social Security numbers, mother's maiden names, passwords or other identifying information in response to unexpected calls or if you are at all suspicious.
- If you get an inquiry from someone who says they represent a company or a government agency, hang up and call the phone number on your account statement, in the phone book, or on the company's or government agency's website to verify the authenticity of the request. You will usually get a written statement in the mail before you get a phone call from a legitimate source, particularly if the caller is asking for a payment.
- Use caution if you are being pressured for information immediately.
- If you have a voice mail account with your phone service, be sure to set a password for it. Some voicemail services are preset to allow access if you call in from your own phone number. A hacker could spoof your home phone number and gain access to your voice mail if you do not set a password.
- Talk to your phone company about call blocking tools and check into apps that you can download to your mobile device. The FCC allows phone companies to block robocalls by default based on reasonable analytics. More information about robocall blocking is available at fcc.gov/robocalls.
Remember to check your voicemail periodically to make sure you aren't missing important calls and to clear out any spam calls that might fill your voicemail box to capacity.
ALERT: There have been media reports of skimmers on ATM’s, gas pumps, and self-check-out terminals in the area.
Here are ways you can protect yourself:
- When paying at gas pumps use the pump that has the closest view to the clerks inside. These are less likely to have a skimmer.
- You often have the option to use the card as a credit or a debit card. If you choose the credit option, you’ll likely be able to avoid entering your PIN.
- Always inspect any ATM that you use. Give the card bezel a tug, look for sticky residue, oddly placed stickers, or holes in the exterior.
- If you have the ability, turn your debit/credit card “off” when not in use. This is coming to FMB in 2020!
- Keep an eye on your accounts. Set up
|
|
|
